Sandboxed Gentoo
Introduction
This article is a guide on installing Gentoo in another Linux distribution (Arch, in this case). Look at it like a BSD Jail. It's...
Top 3 Free Best Antivirus Apps For Android In 2013
Being one of the most popular operating systems for smarphones, Android is a target for malware and viruses. The statistics show that Android accounted...
How to Secure Your Home Network with OpenDNS
OpenDNS is a free DNS alternative to your ISP DNS. It helps you to get faster and as well as safer browsing at absolutely...
Introduction to SSH
Introduction
What is SSH? Why use SSH?
SSH is a network protocol similar to telnet or FTP, yet slightly different because it offers secure data communication....
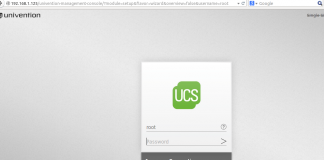
How to install Univention Corporate Server
Preface
Most of the IT or non-IT organization/companies generally possess hybrid environment .i.e. they have Linux based as well as Microsoft based desktops or servers.It...
Protect Your Online Privacy with Tor Browser
Tor (The Onion Router) browser makes things more difficult to trace our Internet activities. Using Tor, we can keep our identity more secure around...
Data Security and Privacy in Cloud Migration
Cloud-based computing has revolutionized the way businesses operate. It provides secure data storage as well as cost-efficient access to vast amounts of information. There...
Pf vs iptables, Untangle, Pfsense – Why not both?
My name is Jacob Graham and I am a Junior Systems Administrator in Victoria, Canada. This will be my first writing for Unixmen and...
How To Avoid Data Surveillance Programs
Probably you've heard about the NSA surveillance program PRISM, XKeyscore and the GCHQ's Tempora. If you did not, you should start looking up for...
Enhancing Security Measures: Best Practices for Linux Servers in WordPress Environments
In the ever-evolving landscape of web development, the synergy between Linux servers and WordPress has become a cornerstone for startups looking to establish a...
Network Monitoring Tools You Have To Know
We all understand how system administrators love to have network monitoring tools which make their lives easier. Following is a list of the best...
Tips to Enhance Linux Security
In recent years, the usage of linux operating systems has increased a bit. Though, not at that impressive rate, there have been more users...
Arachni the Security scanning tool for Web
Introduction:
Arachni is a fully featured web security scanning tool, it is based on ruby framework.It is an open source, modular and high performance tool....
Strengthening Linux Defenses with an Online Cybersecurity Degree
Embracing Next-Level Linux Security Challenges
Linux runs everything from bleeding-edge research clusters to billion-dollar e-commerce backbones, which makes it a fat target for anyone with...
Why I can’t live without Linux
This is written targeting users who might want to try Linux. But also with some facts that Linux users should be aware and feel...
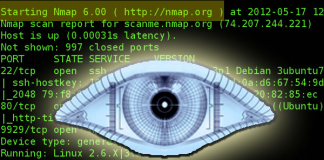
10 Practical Examples Of Linux ‘nmap’ Command
About Nmap
Nmap is a tool used for determining the hosts that are running and what services the hosts are running. Nmap can be a...
The Effect of IT Compliance on Cloud Security
Cloud computing is valuable to businesses that want to increase productivity and become more efficient because it...
How To Install And Use Untangle Firewall
Introduction
Untangle is very lightweight, easy to install and easy to use but very effective firewall operating system. It makes you enable to protect, monitor and...