5 Tips for an Effective Cyber Security Strategy for Your Business
Cyber attacks have drastically advanced, with criminals using more sophisticated tools to steal and misuse company data. This has increased ransomware, phishing attempts, DoS...
6 Factors that Make Linux Important for your Small Business
A huge number of modern companies know about Linux firsthand. Many of them have been using various distributions in one form or another for...
Linux Mint 17.2 ‘Rafaela’ RC is out now. How to Install...
Linux Mint is one of the most popular and extensively used Linux operating system. It mixes the features of Ubuntu and Debain but there...
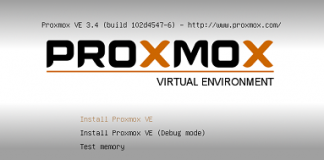
Proxmox Virtual Environment (ProxmoxVE) Is An Open Source Virtualization Solution
Proxmox is an open source and enterprise-ready virtualization solution which lets you create and manage your own virtualization setup. You don’t need to use...
How To Install Ejabberd XMPP Server On CentOS 7
Introduction
Ejabberd is an XMPP application widely used around the globe. It is available on several operating systems but in this article, we will let you know the...
Why Use A Linux Operating System?
In this article, we'll provide some insight into why you should consider using Linux as your operating system. We'll discuss the reasons behind...
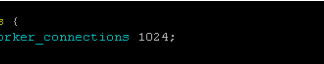
10 Useful Tips To Improve Nginx Performance
Introduction
In this fast paced world where everything is getting online, you can’t afford downtime. Speed and optimization is the most challenging part of ever-evolving computer age. Performance...
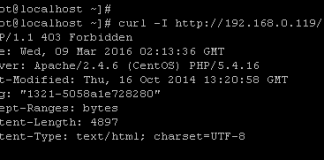
How To Avoid Clickjacking And SlowLoris Attacks On CentOS
What if you come to know that the website you just visited has taken all the confidential data from your laptop/ server / PC?...
Risks to Consider When Using Linux
Linux is a free and open-source operating system that's popular among developers, businesses, and individuals. The flexibility and customizability of Linux make it an...
What is Linear Programming?
Introduction
Linear programming is a method for determining the best solution to a linear function. Making a few simple assumptions is the best technique for...
6 Best Ways to Improve Linux Security
The Linux OS has historically been regarded as more secure than Windows or macOS thanks to how it handles user permissions and because it’s...
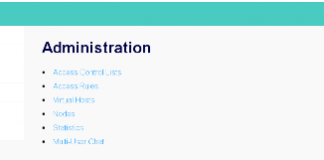
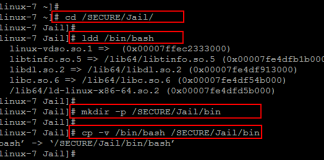
How to Chroot SSH Users on Centos 7
The term chroot refers to a process of creating a virtualized environment in a Unix operating system, separating it from the main operating system...
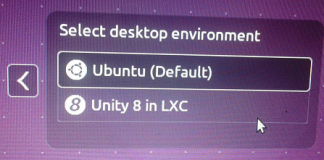
Ubuntu 15.10 Alpha 1 has been released, Installation Guide [...
Introduction
Alpha release of different flavors of upcoming Ubuntu 15.10, also known as Wily Werewolf, are out now just couple of hours ago. Although Ubuntu 15.10...
5 Cybersecurity Tips to Help Linux Users Protect Their Computers
Cybercrime is a growing threat that has caused most internet users to rethink how they protect their data and information. Cybercriminals are getting more...
How to Install Unity 8 Desktop on Ubuntu 15.04
Unity is a well known desktop environment developed by Canonical for Ubuntu specifically. It is well known for features like simplicity, power and integration for...
Install Open Source, Cloud Computing Web Desktop EyeOS on Ubuntu Linux...
EyeOS is just like an online operating system, it is based on cloud computing concept and offers an online desktop based system for collaboration...
Cyber-Attacks on Industrial Infrastructure are Intensifying
Cybercriminals are now attacking the whole world in a very different way. In the past, they were just limited to the normal power users...









![Ubuntu 15.10 Alpha 1 has been released, Installation Guide [ With Screenshots] login ubuntu 10](https://www.unixmen.com/wp-content/uploads/2015/06/login-ubuntu-101-1-324x160.png)