The Best Video Conferencing and Collaboration Platforms for Linux
In the age of remote work, video conferencing and collaboration tools have become essential for staying connected to colleagues, clients, and team members. Fortunately,...
Revolutionizing Video Making with Linux: Unleashing Creative Potential
In today's digital age, videos have become an integral part of our lives. From social media platforms to professional presentations, videos have the power...
Intellectual Property Rights and Linux Development
As we delve into the realm of Linux development, understanding Intellectual Property (IP) Rights becomes critical. Navigating this maze can ensure a fair, respectful,...
6 Benefits of Outsourcing Software Development to Poland
The demand for software developers is at an all-time high, presenting a significant challenge for tech enterprises...
How to Create a Bootable USB from ISO Files
Introduction
Anyone using a PC today has faced issues with their operating system at...
Nc Command in Linux: Tool to Debug Network Issues
The “nc” command is often referred to as “Netcat”. It is a flexible yet robust tool often...
Raspberry Pi Firewall: Step-by-step guide for an easy setup
Not even Raspberry Pi is safe from cyberattacks. This can be attributed to the fact that the tech community is finding innovative ways to...
LUKS: Detailed Guide to Linux Unified Key Setup
LUKS (Linux Unified Key Setup) is the default encryption method for Linux distributions. It provides robust full-disk encryption. If you put security at the...
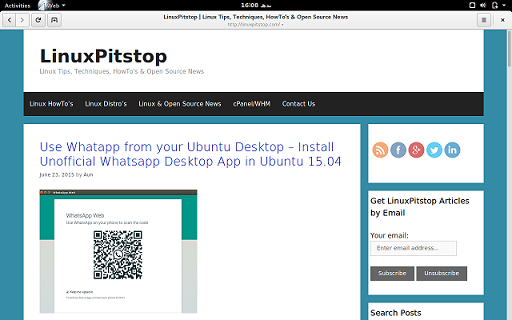
How To Setup OpenEMM On Ubuntu 16.04
Hello and welcome to our todays article in installation setup of OpenEMM on Ubuntu 16.04. OpenEMM is a web-based enterprise application for email marketing,...
How to use the bc command in Linux for Arithmetic Calculations?
The bc command stands for Basic Calculator in Linux. We use the bc command as a command-line calculator. The bc command offers the capabilities...
Linux in education: operating systems for learning and teaching
Nowadays, programming contributes a lot to education to make learning more exciting and easier. We are not only talking about creating many programs like...
How To Use The xxd Hex Dumper Utility In Linux
On most Unix-like operating systems, the xxd command helps users read a file as its hexadecimal values. The ASCII representation of the files is...
How Does Linux Protect Its Users’ Privacy Online?
Internet users are more aware than ever before about the value of their data and how many companies want to collect and use it....
7 Linux Software Trends To Watch In 2023-2024
The stability of Linux is one of the main advantages. The system is known for its reliability and durability, compared to some other operating...
Future of DevOps: Top 6 DevOps Trends in 2024 & Beyond
In recent years, DevOps has emerged as one of the most used software development technology.It is the...
The Linux Command Line: A Tale of Two Tools – apt...
apt vs apt get
Regardless of your preferred Linux distribution, package management is an important function for every...
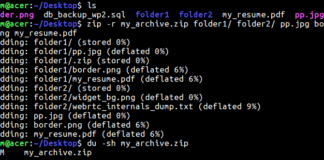
How to Compress Files Using the Linux Zip Command
The Linux zip command is an essential tool for file compression and archiving in Unix-based systems. Whether...
Ubuntu: Install DEB Instructions with Different Methods
DEB (also known as Debian packages) is the primary software package of Ubuntu. DEB packages allow easy...