How to prevent a Supply Chain Attack in a Linux Environment
What is a supply chain attack?
This is a type of cyberattack that seeks to damage an organization by attacking weaker elements in the supply...
Why Use A Linux Operating System?
In this article, we'll provide some insight into why you should consider using Linux as your operating system. We'll discuss the reasons behind...
How VPNs Improve Linux Security
Linux, like Windows, iOS, and macOS, is an operating system. Android runs on the Linux operating system. The operating system, in its most basic...
Best VPNs for Linux with and without GUI
The Linux operating system takes up a tiny portion of the market because it appears daunting to the average person. It’s commonly known as...
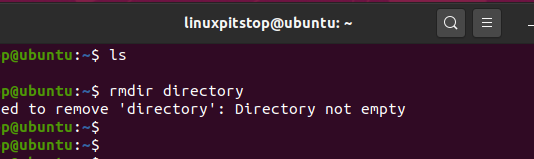
How to Recover Deleted Files in Linux I Guide
Files management is an important skill for everyone who utilizes storage devices for whatever reason. File recovery tools for instance are crucial utilities you...
Enhancing User Experience: How Linux OS and Localization Drive Global Success
In the ever-evolving landscape of technology, user experience (UX) has emerged as a critical factor in determining...
Harnessing the Power of Free VPNs for Enhanced Cybersecurity on Linux
Safeguarding our digital footprint is now crucial in the ever-expanding digital ecosystem where risks to online security...
How to Add User to Sudo Group on Ubuntu 24.04
When you fresh install Ubuntu 24.04 and create a user, that user is added to sudo group...
chmod 755: Understanding File Permissions
What is chmod 755?
The command `chmod 755` is a vital tool in Unix and Unix-like operating systems, used to set specific permissions on files...
How to Install Linux on a Chromebook
Introduction to Linux on Chromebooks
Chromebooks are versatile devices that can be transformed into powerful Linux machines with the right approach. This guide will walk...
AI Software For Linux: Which Linux AI Tools Are Best in...
AI Software For Linux: Which Linux AI Tools Are Best in 2025?
Artificial Intelligence is no longer just a trend; it’s the backbone of every...
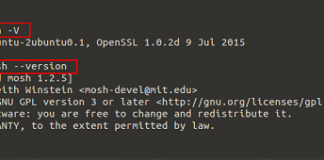
SSH Vs Mosh
Hello everyone, in our today's article we will discuss about the two most prominent Linux/Unix based shell environments that is SSH and Mosh. SSH,...
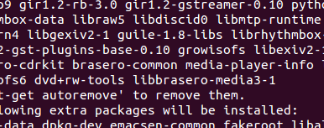
How To Compile And Install OTClient On Ubuntu 16.04
This article is about downloading , compiling and installing the OTClient. We will explain the step by step procedure for downloading, compiling and installing...
What Are the Best Programming Languages for Linux Devs?
If you are on the path to becoming a Linux developer, surely you will understand that computer science and programming are a core part...
How to Install Ubuntu 22.04 LTS (For Beginners)
The “Jammy Jellyfish” version of Ubuntu, version 22.04, was made available on April 21, 2022. The previous release that had Long Term Support was...
Transcription Services on Linux: A Guide to Enhancing Productivity and Efficiency
Transcription services on Linux are becoming increasingly popular, offering users a better way to increase their productivity and efficiency. By leveraging the open-source nature...
.NET and Linux: The Perfect Combination for Modern Software Development Platforms
Introduction
In the past few years, there have been significant advancements in the field of software development. While technologies like .NET and Linux have always...
Why Open Source Operating Systems Are Utilised by Hackers the Most?
The popularity of open source operating systems (OS) is evident in various tech circles. However, it’s intriguing to note how they particularly resonate with...