In today’s ever-evolving cyber threats, organizations must implement robust security measures that safeguard their valuable data and resources. One such essential measure is the Segregation of Duties (SoD). It plays a critical role in mitigating the risks associated with unauthorized access, fraud, and errors.
It’s worth noting that SoD is applicable across various platforms and systems. This article will focus on its implementation in Linux environments using a combination of tools and best practices.
What Is SoD?
Segregation of duties is a key concept in an organization’s internal controls, risk management, and fraud prevention. It divides critical tasks and responsibilities among individuals, departments, or systems.
As such, no single person or entity will have complete control over an entire process or function. It reduces the risk of errors, fraud, or abuse of power.
Segregation of duties can be handy in financial transactions, IT systems, and operational processes. A typical example is separating the responsibilities for approving transactions, recording transactions, and reconciling account balances in the finance department.
Another use case is distributing system development, testing, and deployment roles in IT departments.
Implementation Of SoD In Linux
SoD in a Linux environment involves setting up appropriate access controls and permissions to divide critical tasks among users and groups. Here are the guidelines you should follow:
- Create Well-defined User Roles And Groups
Start by defining clear roles and groups based on job functions, responsibilities, and access requirements. This step ensures that users are only granted the necessary privileges to perform their duties. Use the ‘useradd’ command to create new users and ‘groupadd’ to create new groups. For example:
- useradd -m -s /bin/bash username
- groupadd groupname
- Assign Users To Appropriate Groups
Assign each user to one or more groups according to their responsibilities. It enables you to manage permissions based on group membership, simplifying access rights management.
Use the ‘usermod’ command to add users to groups. For example: usermod -aG groupname username
- Set Up File And Directory Permissions
Configure permissions for files and directories using the ‘chmod’ command to control access based on user roles and groups. Linux file permissions are expressed as a combination of read (r), write (w), and execute (x) permissions for the owner, group, and others.
For example, to grant read and write access to the owner, read access to the group, and no access to others, use chmod 640 filename.
- Use Access Control Lists (ACLs) For Fine-Grained Control
ACLs provide an additional layer of control by allowing you to specify permissions for individual users and groups. To use ACLs, ensure that your file system supports them (e.g., ext4, XFS, or Btrfs) and that they are enabled.
Install the ‘acl’ package, then use the ‘setfacl’ command to set up ACLs. For example:
setfacl -m u:username:rwx,g:groupname:rx directoryname
- Implement Sudo For Privilege Escalation
Sudo allows users to execute commands with elevated privileges, making it easier to implement SoD by limiting the number of users with direct root access. Configure the ‘/etc/sudoers’ file using the ‘visudo’ command and define which commands users are allowed to execute with elevated privileges.
For example, to allow a user to run specific commands as root, add the following line:
username ALL=(ALL:ALL) NOPASSWD: /usr/sbin/command1, /usr/sbin/command2
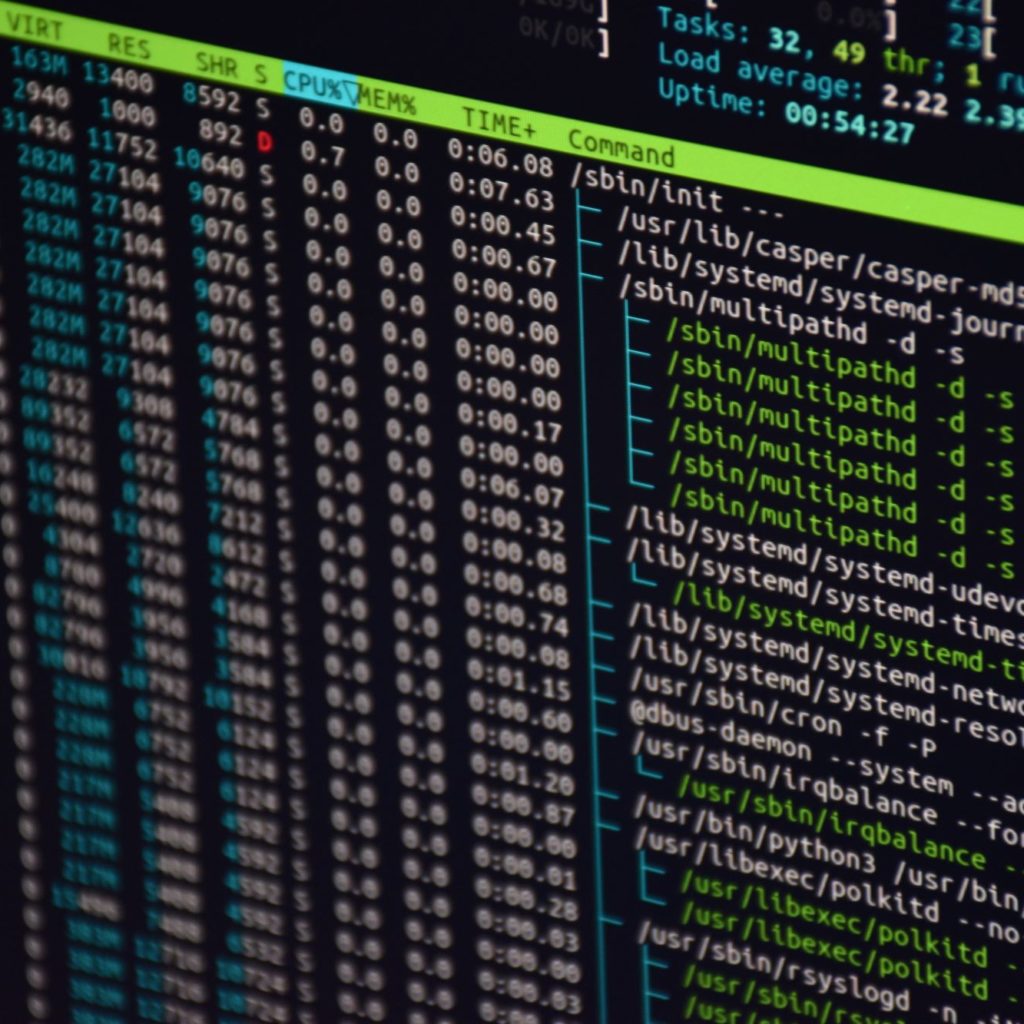
- Monitor And Audit User Activity
Keeping track of system-level events and user actions allow you to detect potential security risks, unauthorized access, and misuse of privileges. Consider the following key points:
- Use the ‘auditd’ daemon: The Linux Auditing Daemon (auditd) is a powerful tool for tracking system-level events and user actions. It collects and stores audit logs that can be used to investigate security incidents and monitor compliance.
- Configure log management tools: Centralizing and managing logs from various sources can significantly simplify monitoring user activity. Logwatch, Logcheck, and Graylog can parse and analyze logs, generate reports, and send alerts for suspicious activities.
- Set up monitoring and alerting: This is essential for detecting and responding to potential security threats. You can configure tools like Nagios, Zabbix, or Prometheus to monitor your Linux systems and send notifications when specific events or anomalies are detected. You can integrate these tools with log management solutions to provide comprehensive monitoring and alerting capabilities.
- Regularly review audit logs: Establish a routine for checking audit logs, paying particular attention to activities involving elevated privileges, sensitive files, and critical system changes.
- Maintain user access records: Maintain up-to-date records of user access permissions, group memberships, and role assignments. This information can be invaluable during audits and investigations, as it helps you understand the context of user actions and determine whether they align with established SoD policies.
Also, train your team members on the importance of SoD and how to monitor and audit user activity. Help them recognize potential security risks, interpret audit logs, and respond to alerts.
Conclusion
Implementing SoD in Linux environments is essential for enhancing your organization’s security posture. Following the tips in this article can help you create well-defined user roles and groups and manage memberships. Adopting these best practices will reduce the risk of unauthorized access and misuse of privileges. It’ll also contribute to creating a secure and reliable environment for your organization.





