My name is Jacob Graham and I am a Junior Systems Administrator in Victoria, Canada. This will be my first writing for Unixmen and I hope that everybody enjoys it as much as I enjoy writing it for you.
Today I will be talking a lot about OpenBSD, FreeBSD and other Unix-like operating systems from the Berkeley Software Distribution. I thought that would be appropriate being my first document on Unixmen. I however will also be talking about Linux and Untangle and how they complement Unix based firewalls such as Pfsense.
I would like to explain what I think is the best way to secure a network from hackers and bots and why these techniques work as well as I say they do. I however will not be explaining how, as I will save that for another article. That being said if there is anything in error here please let me know but I am sure you will find nothing in contrast to common theory. I would also like to show you guys some things I like to do and things I think are critical to IT security.
Pfsense Firewall and Router
Pfsense is a free, open-source customized distribution of the FreeBSD tailored for use as a firewall and router. On top of being a highly powerful, flexible and secure firewall and routing system, it includes a long list of highly useful features and a packages allowing further features without adding a potential security vulnerability to the base. Now telling all of you what I use is a security risk all by itself but that’s just how much I trust this, that being said nothing is really hack proof and security is not really about that. It’s about reducing the attack surface hackers have to play with.
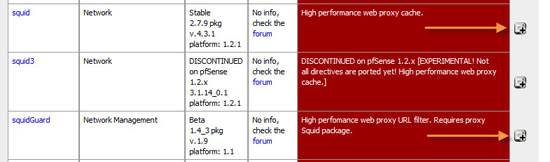
The first thing to do after you have Pfsense set up and you have changed the default username and make everything tight as you can. What you do is make your way to the packages area. You really have to appreciate the packages they have as the features and functionality are unreal.
Untangle-UTM
Untangle is Linux based unlike Pfsense but they both use Snort for Intrusion Detection. Untangle is a also a router but is classified as a UTM. A Unified Threat Management system or UTM is the new kid on the block in security but has been around for over a decade.
In theory, UTM is an evolution of the traditional firewall into an all in one security product able to perform multiple security functions in a single system: network firewalling, network intrusion prevention and gateway antivirus , gateway anti-spam, content filtering, data leak prevention, load balancing, and appliance reporting.
So why is pf better?
So what makes Pfsense better than say Smoothwall or Untangle? Well this is a big argument, however here is my reasons. It comes down to iptables vs pf or packet filter – Pfsense uses pf.conf and Linux based Routers use Netfilter and iptables. iptables is faster, but isn’t as secure – it doesn’t do true stateful inspection and has had quite a number of bugs. iptables mighty be more flexible in certain circumstances (e.g. places in the IP stack that you can insert filtering rules), but the security appeals to me over the additional flexibility.
Back in 2009-2010 I saw a defcon about hacking routers with “DNS Rebinding” and in less than a months time Pfsense has contacted the man who gave the defcon presentation and mentioned they had fixed it. Many routers still do not even address this issue being that it’s actually flawed in DNS itself.
The major advantage that PF has over iptables is the separation of mechanism from the policy. iptables requires you enter rules through a CLI program with variable and convoluted arguments that require extra kernel modules. PF is a text format with a better parser – very powerful with a low overhead.
Snort – IDS/IPS/NIDS
Snort is a free and open-source network intrusion prevention system (NIPS) and network intrusion detection system (NIDS) created by Martin Roesch in 1998. Snort is now developed by Sourcefire, of which Roesch is the founder and CTO. In 2009, Snort entered InfoWorld‘s Open Source Hall of Fame as one of the “greatest [pieces of] open-source software of all time”. Snort is also the de-facto standard in security and has many Fortune 500 companies that claim they use it.
OpenBSD
OpenBSD has had less than 2 security vulnerabilities in over 12 years with the default install. Ubuntu has a half a dozen a year and Windows OS, is even worse.
So many people actually make there own pf.conf firewalls with OpenBSD as they are even more secure. However, some would argue OpenBSD is not even an OS being the attack surface is to small to be considered an ‘Operating System’. So this is another option I wanted to share as it is a little better.
Rule Processing
Filtering rules are the two main things here that need to be taken into consideration. iptables has various tables at play, each with different chains that packets traverse, whereas pf just processes the packets straight down to the config file. Where as with pf, packets traverse the flat pf.conf file itself. Even if a single packet matches a rule, it continues to process the packet down to the whole configuration file. Only if a rule contains the “quick” option does pf stop the actual processing and take action before hitting the end of the set of rules. On the other hand if a packet makes it all the way to the end of the config file, the last action specified from a rule that matched this packet is taken.
With iptables things are different, packets are processed by various “chains” in different order, depending on the source and destination in the actual packet. For example, normal outgoing packets are processed by the output chain on the table. Rules within this chain can create processing to jump over to a different set of rules on a user-defined chain for example, or might even take such an action on a packet. When a packet matches a rule, processing on that chain stops without hesitation and the action is taken into effect. IDS/IPS (Intrusion Detection system) (Intrusion Protection System) An IDS detects an intrusion and logs it, an IPS stops it in its tracks.
The Best of Both Worlds
What I like to do is not fully going to be covered as this could go for miles. I set up a harden Pfsense firewall and simply set up a Untangle machine in whats called “Bridge Mode”. The Untangle UTM basically scans and filters once again everything the Pfsense router has just passed along as safe packets. So this is by definition a two filter system. We have the security of both PF and iptables in what known as a layered approach. I find this works really well and many may consider it a Tin Foil Hat network.
This concludes what I do with firewalls alone and I hope you enjoyed it.






