About Nmap
Nmap is a tool used for determining the hosts that are running and what services the hosts are running. Nmap can be a valuable diagnostic tool for network administrators while they can be also a potent reconnaissance tool for the Black-hat community (Hackers, Crackers, Script Kiddies, etc). Once the network is charted out using tools like Lan MapShot, the Nmap can be used to determine the type of services and hosts running in the network.
In this article, we will cover some useful practical examples of Linux namp command. The primary Uses of nmap is:
- Determining open ports and services running in an host
- Determine the Operating System running on a host
- Alter the source IP of the scan (One way is to use –S option)
Install Nmap
To install the namap command under Ubuntu/Debian open your terminal and type this command:
sudo apt-get install nmap
And to install nmap under Centos/Redhat you can use this command.
sudo yum install nmap
After installing nmap in your linux server, we will see the 10 practical examples of this awesome command.
Discover IP’s in a subnet
This is one of the simplest uses of nmap. This command is commonly refereed to as a “ping scan”, and tells nmap to send an icmp echo request, TCP SYN to port 443, TCP ACK to port 80 and icmp timestamp request to all hosts in the specified subnet.
Then you will a list of hosts with there ip responded.
$ nmap -sP 172.16.0.0/24
Starting Nmap 5.21 ( http://nmap.org ) at 2015-06-23 09:37 EST
Nmap scan report for 172.16.0.1
Host is up (0.0010s latency).
Nmap scan report for 172.16.0.95
Host is up (0.0031s latency).
Nmap scan report for 172.16.0.110
Host is up (0.0018s latency).
Check and Scan for open ports
This command is the default use of nmap. It will take time to give you response as nmap will attempt a TCP SYN connection to 1000 of the most common ports as well as an icmp echo request to determine if a host is up. nmap will also perform a DNS reverse lookup on the identified ip’s as this can sometimes be useful information.
$ nmap 172.16.0.0/24
Starting Nmap 5.21 ( http://nmap.org ) at 2015-06-23 09:39 EST
Nmap scan report for 172.16.0.1
Host is up (0.0043s latency).
Not shown: 998 closed ports
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
443/tcp open https
Identify the Operating System of a host
To identify the operating system of a host using nmap, you can do it with option -O. But the operating system scan does require root privileges.
# nmap -O 172.16.0.15
Starting Nmap 5.21 ( http://nmap.org ) at 2015-06-23 09:49 EST
Nmap scan report for 172.16.0.15
Host is up (0.00032s latency).
Not shown: 996 closed ports
PORT STATE SERVICE
88/tcp open kerberos-sec
139/tcp open netbios-ssn
445/tcp open microsoft-ds
631/tcp open ipp
MAC Address: 00:00:00:00:00:00 (Unknown)
Device type: general purpose
Running: Apple Mac OS X 10.5.X
OS details: Apple Mac OS X 10.5 - 10.6 (Leopard - Snow Leopard) (Darwin 9.0.0b5 - 10.0.0)
Network Distance: 1 hop
Identify Hostnames
Also namp allows you to find hostnames for all of the ip’s in a subnet without having send a packet to the individual hosts themselves.
option tells nmap to do a simple DNS query for the specified ip. This scan doesn’t require root privileges.
$ nmap -sL 172.16.0.0/24
Starting Nmap 5.21 ( http://nmap.org ) at 2015-06-23 09:59 EST
Nmap scan report for 172.16.0.0
Nmap scan report for router.local (172.16.0.1)
Nmap scan report for myhost.local (172.16.0.2)
Nmap scan report for another.myhost.local (172.16.0.3)
Scan TCP and UDP port
This command nmap -sS -sU -PN will check about 2000 common tcp and udp ports to see if they are responding. When you use the option
nmap will skip the ping scan and assume the host is up. This can be useful to check if a firewall prevent icmp replies. But this scan require a root privileges.
# nmap -sS -sU -PN 172.16.0.16
Starting Nmap 5.21 ( http://nmap.org ) at 2015-06-23 10:25 EST
Nmap scan report for 172.16.0.16
Host is up (0.00029s latency).
Not shown: 1494 closed ports, 496 filtered ports
PORT STATE SERVICE
88/tcp open kerberos-sec
139/tcp open netbios-ssn
445/tcp open microsoft-ds
631/tcp open ipp
88/udp open|filtered kerberos-sec
123/udp open ntp
137/udp open netbios-ns
138/udp open|filtered netbios-dgm
631/udp open|filtered ipp
5353/udp open zeroconf
Scan for all ports TCP and UDP
This command require a root privileges and it is the same as above however by specifying the full port range from 1 to 65535 nmap will scan to see if the host is listening on all available ports. You can use the port range specification on any scan that performs a port scan.
# nmap -sS -sU -PN -p 1-65535 172.16.0.14
Starting Nmap 5.21 ( http://nmap.org ) at 2015-06-23 10:18 EST
Nmap scan report for 172.16.0.14
Host is up (0.00029s latency).
Not shown: 131052 closed ports
PORT STATE SERVICE
88/tcp open kerberos-sec
139/tcp open netbios-ssn
445/tcp open microsoft-ds
631/tcp open ipp
17500/tcp open unknown
88/udp open|filtered kerberos-sec
123/udp open ntp
137/udp open netbios-ns
138/udp open|filtered netbios-dgm
631/udp open|filtered ipp
5353/udp open zeroconf
17500/udp open|filtered unknown
51657/udp open|filtered unknown
54658/udp open|filtered unknown
56128/udp open|filtered unknown
57798/udp open|filtered unknown
58488/udp open|filtered unknown
60027/udp open|filtered unknown
Scan TCP Connection
This command will ask the OS to establish a TCP connection to the 1000 common ports.
$ nmap -sT 172.16.0.14
Starting Nmap 5.21 ( http://nmap.org ) at 2015-06-23 10:48 EST
Nmap scan report for 172.16.0.14
Host is up (0.0014s latency).
Not shown: 964 closed ports, 32 filtered ports
PORT STATE SERVICE
88/tcp open kerberos-sec
139/tcp open netbios-ssn
445/tcp open microsoft-ds
631/tcp open ipp
Fast Scan
You can use this scan to check the the most common 100 ports.
$ nmap -T4 -F 172.16.0.14
Starting Nmap 6.01 ( http://nmap.org ) at 2015-06-23 10:49 EST
Nmap scan report for 172.16.0.14
Host is up (0.00047s latency).
Not shown: 96 closed ports
PORT STATE SERVICE
88/tcp open kerberos-sec
139/tcp open netbios-ssn
445/tcp open microsoft-ds
631/tcp open ipp
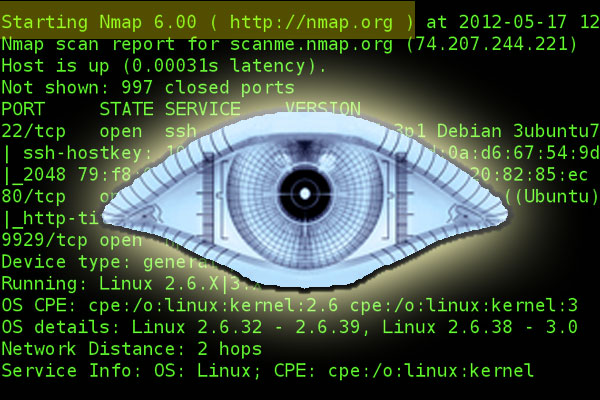
Aggressive and obtrusive Scan
Not like the earlier commands this scan is very aggressive and very obtrusive. The option
tell nmap to perform OS checking and version checking. The
is for the speed template, these templates are what tells nmap how quickly to perform the scan.
$ nmap -T4 -A 172.16.0.0/24
Nmap scan report for 172.16.0.9
Host is up (0.00060s latency).
Not shown: 996 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 5.9p1 Debian 5ubuntu1 (protocol 2.0)
| ssh-hostkey: 1024 00:00:00:00:00:00:00:00:00:00:00:00:00:00:00:6c (DSA)
|_2048 00:00:00:00:00:00:00:00:00:00:00:00:00:00:00:6c (RSA)
80/tcp open http nginx 1.1.19
|_http-title: 403 Forbidden
|_http-methods: No Allow or Public header in OPTIONS response (status code 405)
111/tcp open rpcbind
| rpcinfo:
| program version port/proto service
| 100000 2,3,4 111/tcp rpcbind
| 100000 2,3,4 111/udp rpcbind
| 100003 2,3,4 2049/tcp nfs
| 100003 2,3,4 2049/udp nfs
| 100005 1,2,3 46448/tcp mountd
| 100005 1,2,3 52408/udp mountd
| 100021 1,3,4 35394/udp nlockmgr
| 100021 1,3,4 57150/tcp nlockmgr
| 100024 1 49363/tcp status
| 100024 1 51515/udp status
| 100227 2,3 2049/tcp nfs_acl
|_ 100227 2,3 2049/udp nfs_acl
2049/tcp open nfs (nfs V2-4) 2-4 (rpc #100003)
Service Info: OS: Linux; CPE: cpe:/o:linux:kernel
Verbose
The last command is verbose.When you add verbose to the commands line above you will get a better info into what nmap is doing and checking like this example:
$ nmap -T4 -A -v 172.16.0.16
Starting Nmap 6.01 ( http://nmap.org ) at 2015-06-23 12:50 EST
NSE: Loaded 93 scripts for scanning.
NSE: Script Pre-scanning.
Initiating Ping Scan at 12:50
Scanning 192.168.0.164 [2 ports]
Completed Ping Scan at 12:50, 0.00s elapsed (1 total hosts)
Initiating Parallel DNS resolution of 1 host. at 12:50
Completed Parallel DNS resolution of 1 host. at 12:50, 0.01s elapsed
Initiating Connect Scan at 12:50
Scanning 192.168.0.164 [1000 ports]
Discovered open port 139/tcp on 172.16.0.16
Discovered open port 445/tcp on 172.16.0.16
Discovered open port 88/tcp on 172.16.0.16
Discovered open port 631/tcp on 172.16.0.16
Completed Connect Scan at 12:50, 5.22s elapsed (1000 total ports)
Initiating Service scan at 12:50
Scanning 4 services on 172.16.0.16
Completed Service scan at 12:51, 11.00s elapsed (4 services on 1 host)
NSE: Script scanning 172.16.0.16.
Initiating NSE at 12:51
Completed NSE at 12:51, 12.11s elapsed
Nmap scan report for 172.16.0.16
Host is up (0.00026s latency).
Not shown: 996 closed ports
PORT STATE SERVICE VERSION
88/tcp open kerberos-sec Mac OS X kerberos-sec
139/tcp open netbios-ssn Samba smbd 3.X (workgroup: WORKGROUP)
445/tcp open netbios-ssn Samba smbd 3.X (workgroup: WORKGROUP)
631/tcp open ipp CUPS 1.4
| http-methods: GET HEAD OPTIONS POST PUT
| Potentially risky methods: PUT
|_See http://nmap.org/nsedoc/scripts/http-methods.html
| http-robots.txt: 1 disallowed entry
|_/
Service Info: OS: Mac OS X; CPE: cpe:/o:apple:mac_os_x
We’ve almost covered all the options available in the namp command. If we’ve still missed any options and you would like to include in this list, please update us via comment box. Thank you 🙂