Steg is a cross-platform portable software written in C++ which is used to hide your confidential data inside compressed or uncompressed images. It supports JPEG (JPG), TIFF, PNG, BMP image formats. It comes with a GUI interface and you don’t have to install it. Just download the software, extract and use it.
Getting Steg
Download the Steg software here. Or use the following command to download.
For 32bit systems:
sk@sk:~$ wget https://googledrive.com/host/0B-_yxJMDtRxyRDNGNk1YcXR0UTg/steg-v1.0.0.2-linux32.tgz
For 64bit systems:
sk@sk:~$ wget https://googledrive.com/host/0B-_yxJMDtRxyUExLZzZ3S2VDbjQ/steg-v1.0.0.2-linux64.tgz
Run Steg
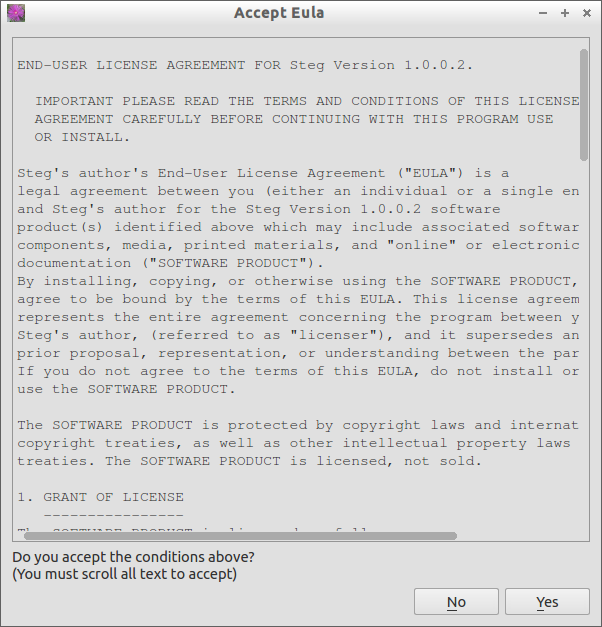
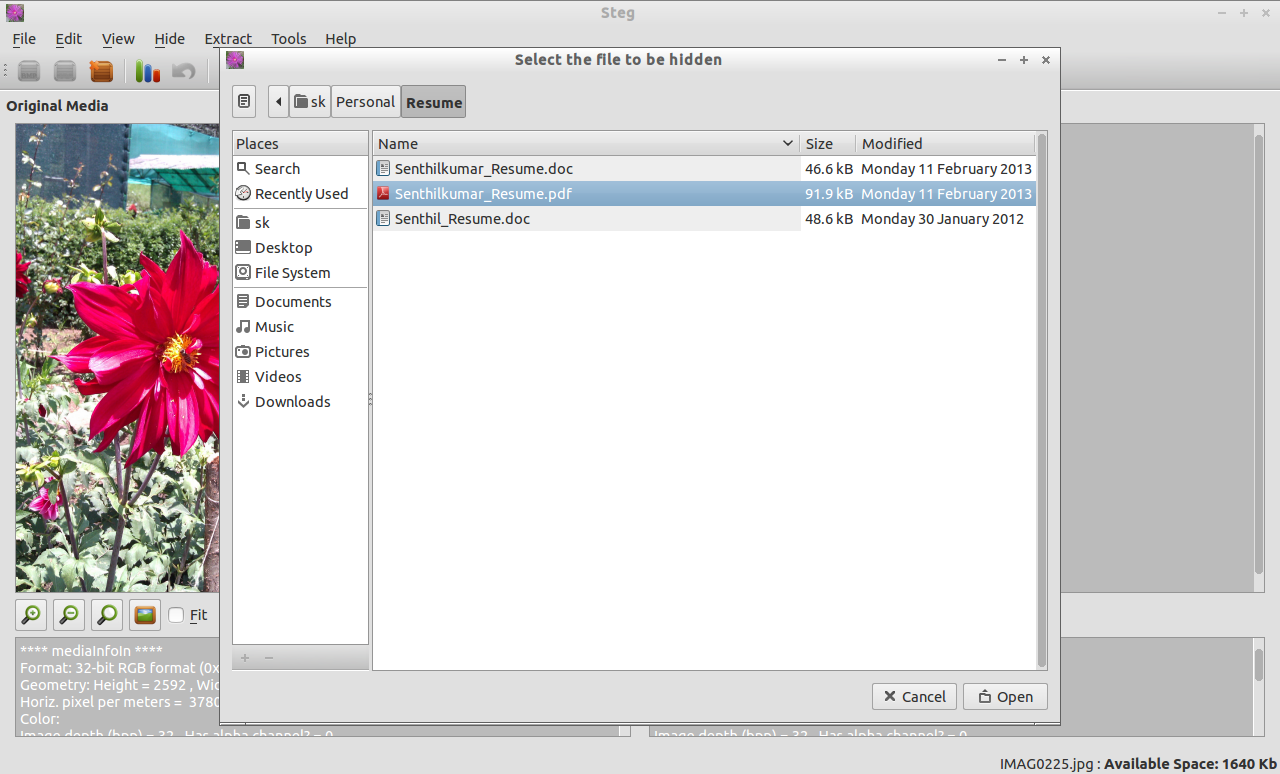
Extract the zip file that you have downloaded. Open the executable file called steg in the extracted folder. Accept the License Agreement.
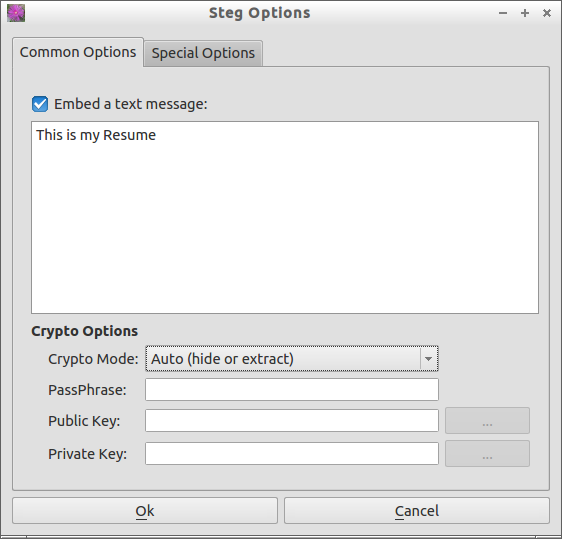
Cryptography Modes
Steg gives the following cryptography methods.
Auto:
The data will be encrypted but no PassPhrase or keys will be required to extract data.
Symmetric:
when you hide data, data will be encrypted with the provided PassPhrase and the same PassPhrase is required to extract.
Asymmetric unsigned:
when you want to hide data (you are the sender) only the receiver’s public key is required. When you want to extract data (you are the receiver) only your private key is required.
Asymmetric signed:
when you want to hide data (you are the sender) the receiver’s public key and your private key are required. When you want to extract data (you are the receiver) only your private key is required but the sender’s public key is requested. If you don’t provide the sender’s public key, at the end of the the extraction process, you will be warned that the sender identity is not verified. If you provide the sender’s public key you will be informed if sign verification is succeeded.
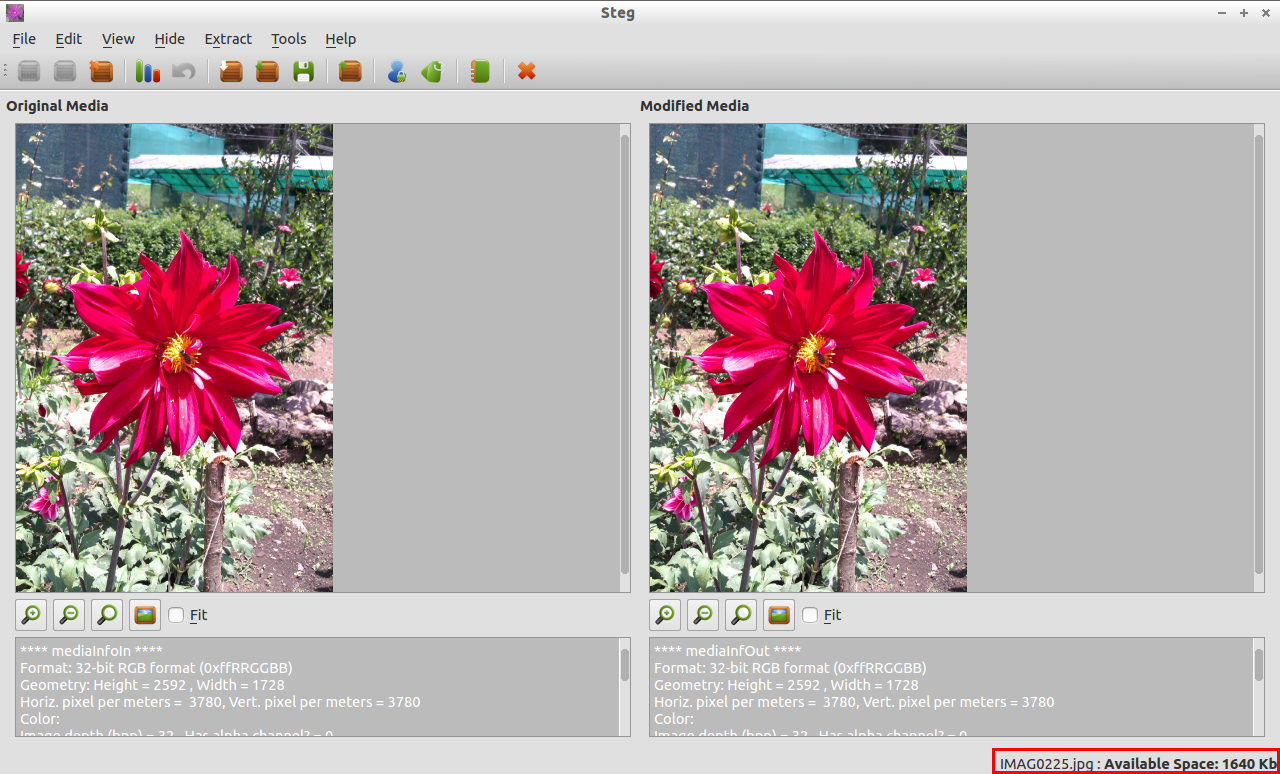
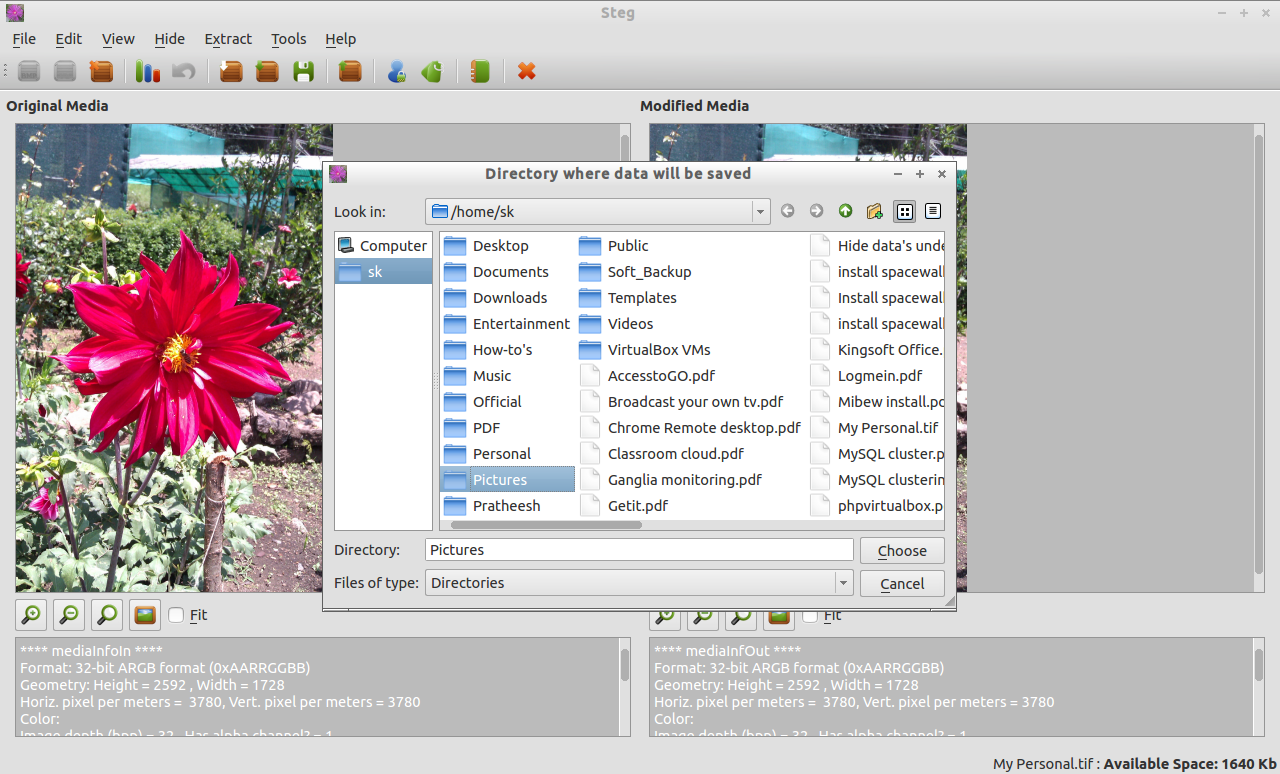
Finally click on Save button in the Tool bar to save the encrypted image. Enter the file name to save.

For information about Steg, i suggest you to read the official manual page.