Introduction
This article is a guide on installing Gentoo in another Linux distribution (Arch, in this case). Look at it like a BSD Jail. It’s not a true install, merely a chroot–a virtual machine.
Why, you ask? I think we’re all aware of and experienced with visualization technology. One of its drawbacks is that the user is unable to utilize all the resources of the running system. If one is not very comfortable with installing a distribution like Gentoo, this is a very good way of familiarizing yourself. You’ll optimize it for your system, not a VBox hard drive. So it can be ported as a true install to your computer if you need it using dd.
Not all of us have spare systems to test on, you know!
Requirements
- A running Linux environment (obviously)
- Gentoo Stage 3 tarball
- Portage tarball
- Free space (15-20 GB will be enough)
You can get the tarballs from gentoo.org. Head over to the “mirrors” hyperlink and select the one closest to you.
For the Stage 3 tarball, go to Architecture > current-stage3 and download the latest .tar.bz2 file.
To get the portage tarball (portage is Gentoo’s package manager, by the way), click on Snapshots and download the latest .tar.bz2 or tar.xz file. It’s worth noting that the xz files are more compressed in comparison to bz2.
Starting the installation
First of all, we need to create a virtual hard drive to hold all that data. For this purpose, we will use dd. dd is a utility which dumps data crudely from a source to a target:
$ dd if=/dev/zero of=gentoo.img bs=1M count=0 seek=30720
In the example above, I have create a img file of size 30720MB (30 GB) which contains nothing at all. It exists in the current working directory.
Now, we format it to a file system of our requirements. I have used ext4:
$ mkfs.ext4 gentoo.img
Create a mount point for your Gentoo jail. I am using ~/gentoo:
$ mkdir ~/gentoo
Mount the .img file:
$ mount -o loop gentoo.img ~/gentoo
Navigate to that directory and become root:
$ cd ~/gentoo && su
Instead of using ‘su’ once and getting root privileges until you exit, you can also use ‘sudo’ per command. It is safer, just 2 characters more per command.
From now on, you should see a hash (#) before a command. This will mean that it is supposed to be executed as root.
Decompress the stage3 tarball:
# tar xfv /path/to/stage3
I don’t use a compression filter argument like -j or -x because I can’t remember them and tar is smart enough to find it on its own.
Jump to that ‘usr‘ directory which is inside ~/gentoo and unzip portage:
# cd usr
# tar xfv /path/to/portage
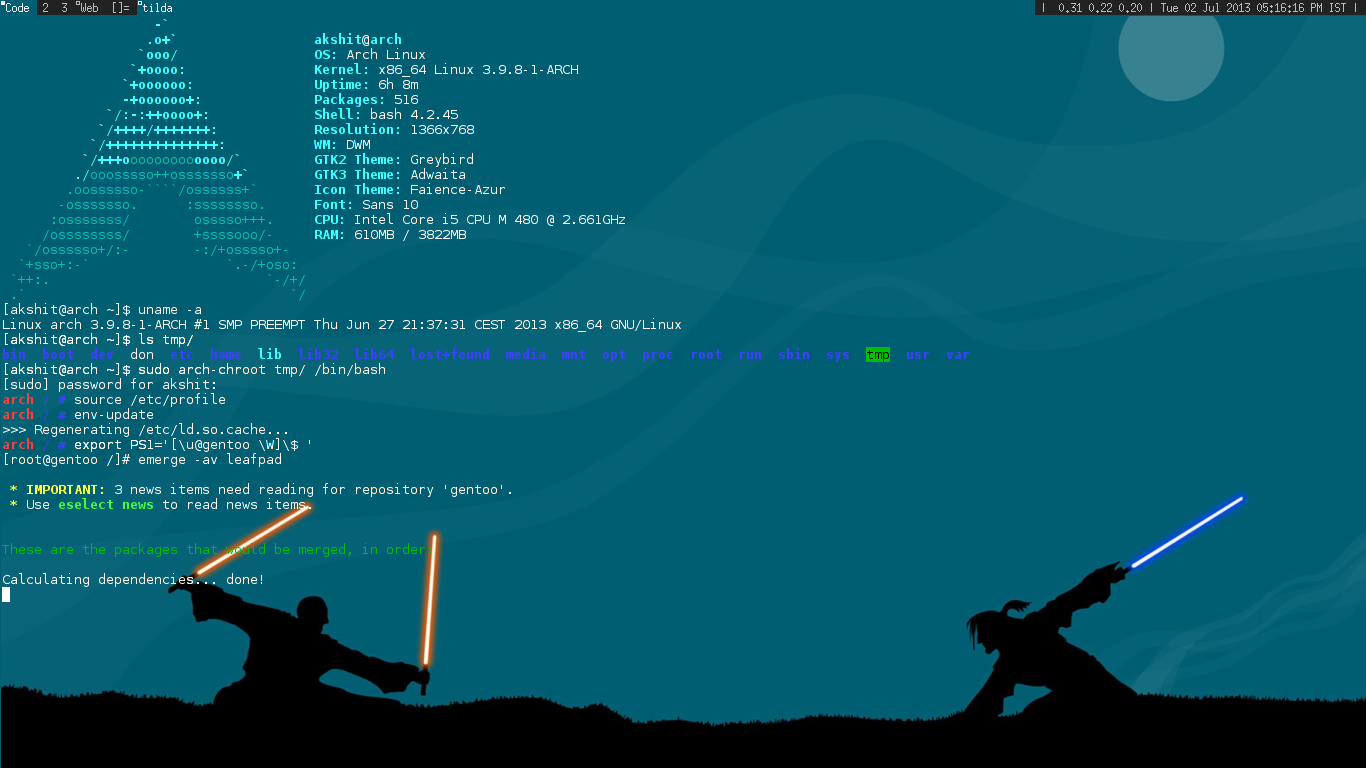
Chrooting into the base install (finally… )
Copy /etc/resolv.conf from your system to your mountpoint:
# cp /etc/resolv.conf ~/gentoo/etc/resolv.conf
There are multiple ways to chroot. One is the conventional way – chroot /path/to/root /bin/shell
With this, you’ll have to mount all the temporary file systems manually. So let me introduce you to arch-install-scripts.
Arch users can just install arch-install-scripts from the official repositories and ignore the rest. Others have two choices, either to download arch-chroot from the arch-install-scripts package or carry on normally.
Note: After chrooting, you do not need to use use ‘su’ or ‘sudo’
arch-chroot users:
# arch-chroot ~/gentoo /bin/bash
Others:
# mount -o bind /dev ~/gentoo/dev
# mount -t proc none ~/gentoo/proc
# chroot ~/gentoo /bin/bash
Load /etc/profile:
source /etc/profile && env-update
Define a PS1:
export PS1='[\u@gentoo \W]\$
Congratulations! You’re in your base Gentoo system.
A few tips
You can also mount your host’s /usr/src in your chroot system to take advantage of kernel sources (which your Gentoo system will use a lot, trust me).
# mount -o bind /usr/src ~/gentoo/usr/src
This step needs to be taken before chrooting.
Since portage has a pretty huge cache, I suggest that you mount that in your host system as well if you’re using a .img file of a smaller size.
Enjoy Gentoo-ing!