Denial-of-Service (DoS) attack is an attempt to make a machine or network resource unavailable to its intended users, such as to temporarily or indefinitely interrupt or suspend services of a host connected to the Internet. A distributed denial-of-service (DDoS) is where the attack source is more than one–and often thousands of-unique IP addresses.
What is mod_evasive?
mod_evasive is an evasive maneuvers module for Apache to provide evasive action in the event of an HTTP DoS or DDoS attack or brute force attack. It is also designed to be a detection and network management tool, and can be easily configured to talk to ipchains, firewalls, routers, and etcetera. mod_evasive presently reports abuses via email and syslog facilities.
Installing mod_evasive
- Server Distro: Debian 8 jessie
- Server IP: 10.42.0.109
- Apache Version: Apache/2.4.10
mod_evasive appears to be in the Debian official repository, we will need to install using apt
# apt-get update # apt-get install libapache2-mod-evasive
Setting up mod_evasive
We have mod_evasive installed but not configured, mod_evasive config is located at /etc/apache2/mods-available/evasive.conf. We will be editing that which should look similar to this
<IfModule mod_evasive20.c> #DOSHashTableSize 3097 #DOSPageCount 2 #DOSSiteCount 50 #DOSPageInterval 1 #DOSSiteInterval 1 #DOSBlockingPeriod 10 #DOSEmailNotify you@yourdomain.com #DOSSystemCommand "su - someuser -c '/sbin/... %s ...'" #DOSLogDir "/var/log/mod_evasive" </IfModule>
mod_evasive Configuration Directives
- DOSHashTableSize
This directive defines the hash table size, i.e. the number of top-level nodes for each child’s hash table. Increasing this number will provide faster performance by decreasing the number of iterations required to get to the record, but will consume more memory for table space. It is advisable to increase this parameter on heavy load web servers. - DOSPageCount:
This sets threshold for total number of hits on same page (or URI) per page interval. Once this threshold is reached, the client IP is locked out and their requests will be dumped to 403, adding the IP to blacklist - DOSSiteCount:
This sets the threshold for total number of request on any object by same client IP per site interval. Once this threshold is reached, the client IP is added to blacklist - DOSPageInterval:
The page count interval, accepts real number as seconds. Default value is 1 second - DOSSiteInterval:
The site count interval, accepts real number as seconds. Default value is 1 second - DOSBlockingPeriod:
This directive sets the amount of time that a client will be blocked for if they are added to the blocking list. During this time, all subsequent requests from the client will result in 403 (Forbidden) response and the timer will be reset (e.g. for another 10 seconds). Since the timer is reset for every subsequent request, it is not necessary to have a long blocking period; in the event of a DoS attack, this timer will keep getting reset.The interval is specified in seconds and may be a real number. - DOSEmailNotify:
This is an E-mail if provided will send notification once an IP is being blacklisted - DOSSystemCommand:
This is a system command that can be executed once an IP is blacklist if enabled. Where %s is the blacklisted IP, this is designed for system call to IP filter or other tools - DOSLogDir:
This is a directory where mod_evasive stores it’s log
This configuration is what I’m using which is working well and I recommend it if you don’t know how to go about the configuration
<IfModule mod_evasive20.c> DOSHashTableSize 2048 DOSPageCount 5 DOSSiteCount 100 DOSPageInterval 1 DOSSiteInterval 2 DOSBlockingPeriod 10 DOSEmailNotify you@yourdomain.com #DOSSystemCommand "su - someuser -c '/sbin/... %s ...'" DOSLogDir "/var/log/mod_evasive" </IfModule>
As you’ll replace you@yourdomain.com with your email. Since mod_evasive doesn’t create the log directory automatically, we are to create it for it:
# mkdir /var/log/mod_evasive # chown :www-data /var/log/mod_evasive # chmod 771 /var/log/mod_evasive
Once setup is done, make sure mod_evasive is enabled by typing:
# a2enmod evasive
Restart Apache for changes to take effect
# systemctl restart apache2
Testing mod_evasive Setup
mod_evasive set up correctly, now we are going to test if our web server has protection again DoS attack using ab (Apache Benchmark). Install ab if you don’t have it by typing:
# apt-get install apache2-utils
Current stat of our /var/log/mod_evasive
root@debian-server:/var/log/mod_evasive# ls -l total 0 root@debian-server:/var/log/mod_evasive#
We will now send bulk requests to the server, causing a DoS attack by typing:
# ab -n 100 -c 10 http://10.42.0.109/
This is ApacheBench, Version 2.3 <$Revision: 1604373 $> Copyright 1996 Adam Twiss, Zeus Technology Ltd, http://www.zeustech.net/ Licensed to The Apache Software Foundation, http://www.apache.org/ Benchmarking 10.42.0.109 (be patient).....done Server Software: Apache/2.4.10 Server Hostname: 10.42.0.109 Server Port: 80 Document Path: / Document Length: 11104 bytes Concurrency Level: 10 Time taken for tests: 0.205 seconds Complete requests: 100 Failed requests: 70 (Connect: 0, Receive: 0, Length: 70, Exceptions: 0) Non-2xx responses: 70 Total transferred: 373960 bytes HTML transferred: 353140 bytes Requests per second: 488.51 [#/sec] (mean) Time per request: 20.471 [ms] (mean) Time per request: 2.047 [ms] (mean, across all concurrent requests) Transfer rate: 1784.01 [Kbytes/sec] received Connection Times (ms) min mean[+/-sd] median max Connect: 0 1 1.5 1 7 Processing: 3 15 28.0 10 177 Waiting: 2 14 28.0 9 176 Total: 3 17 28.4 12 182 Percentage of the requests served within a certain time (ms) 50% 12 66% 13 75% 14 80% 15 90% 18 95% 28 98% 175 99% 182 100% 182 (longest request)
Sending 100 request on 10 concurrent requests per request, the current stat of my /var/log/mod_evasive directory is now
root@debian-server:/var/log/mod_evasive# ls -l total 4 -rw-r--r-- 1 www-data www-data 5 Dec 15 22:10 dos-10.42.0.1
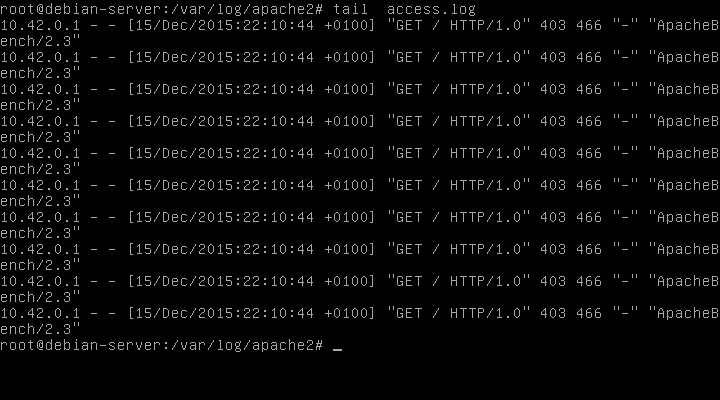
Checking Apache access logs at /var/log/apache2/access.log we can see all connections from ApacheBench/2.3 were dropped to 403:
You see, with mod_evasive you can reduce the attack of DoS. Something that Nginx doesn’t have 😉