Best VPNs for Linux with and without GUI
The Linux operating system takes up a tiny portion of the market because it appears daunting to the average person. It’s commonly known as...
Network Monitoring Tools You Have To Know
We all understand how system administrators love to have network monitoring tools which make their lives easier. Following is a list of the best...
Enhancing Linux Security with Network Access Control Software: Safeguarding Your Networks...
In an era where cyber threats continue to evolve, ensuring the security of computer networks and sensitive data is paramount. As a widely used...
Tips to Enhance Linux Security
In recent years, the usage of linux operating systems has increased a bit. Though, not at that impressive rate, there have been more users...
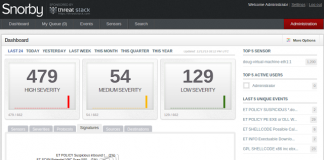
Security Onion: A Linux Distro For IDS, NSM, And Log Management
Introduction
Security Onion is a Linux distribution for intrusion detection, network security monitoring, and log management. It’s based on Ubuntu and contains Snort, Suricata, Bro,...
Security Measures To Protect Your Servers
Introduction
External and internal attackers day after day are menacing your networks. Many intelligent methods are discovered in order to get access and damage your...
5 Most Common Cyber Attacks In 2023
Building a company and keeping it afloat amidst financial turmoil is challenging, and it isn’t made any easier by the number of hackers who...
ufw Firewall Usage on Ubuntu
There's an important piece of software sitting on your computer that you are probably completely unaware that it's even there. Or you simply take...
Privilege-escalation bug present for 9 years in Linux
Under active exploit
There is a critical bug, Dirty COW, present virtually on all GNU/Linux distributions, under active exploit since 9 years ago.
Security researchers, while...
Why I can’t live without Linux
This is written targeting users who might want to try Linux. But also with some facts that Linux users should be aware and feel...
A Secure Password
The minimum you can do to protect yourself is to avoid weak passwords. In most cases people do not know what weak passwords are...
Top 3 Free Best Antivirus Apps For Android In 2013
Being one of the most popular operating systems for smarphones, Android is a target for malware and viruses. The statistics show that Android accounted...
A Pentesting Release for the Raspberry Pi
The Raspberry Pi is a credit-card-sized single-board computer developed in the UK by the Raspberry Pi Foundation with the intention of promoting the teaching...
How To Install Linux Kernel 3.12.4 In Ubuntu
Linux Kernel 3.12.4 has been officially released with fixes for inet6_init() cleanup order, seqlock deadlock in ip6_finish_output2 and Report Descriptor for Logitech MOMO Force. In this...
How to Protect apache directories with a password in Ubuntu
Question : How to Protect apache directories with a password in Ubuntu?
Answer:
To enable this option we have to use 2 terms .htaccess and ...
Cybersecurity And Its Importance For Businesses
It seems that more of our lives are starting to take place online. We use the internet for business, shopping, entertainment, socializing, and so...